How to Choose the Right Compliance Framework for Your Business
How to Choose the Right Compliance Framework for Your Business
How to Choose the Right Compliance Framework for Your Business
>How to Choose the Right Compliance Framework for Your Business
How to Choose the Right Compliance Framework for Your Business
How to Choose the Right Compliance Framework for Your Business

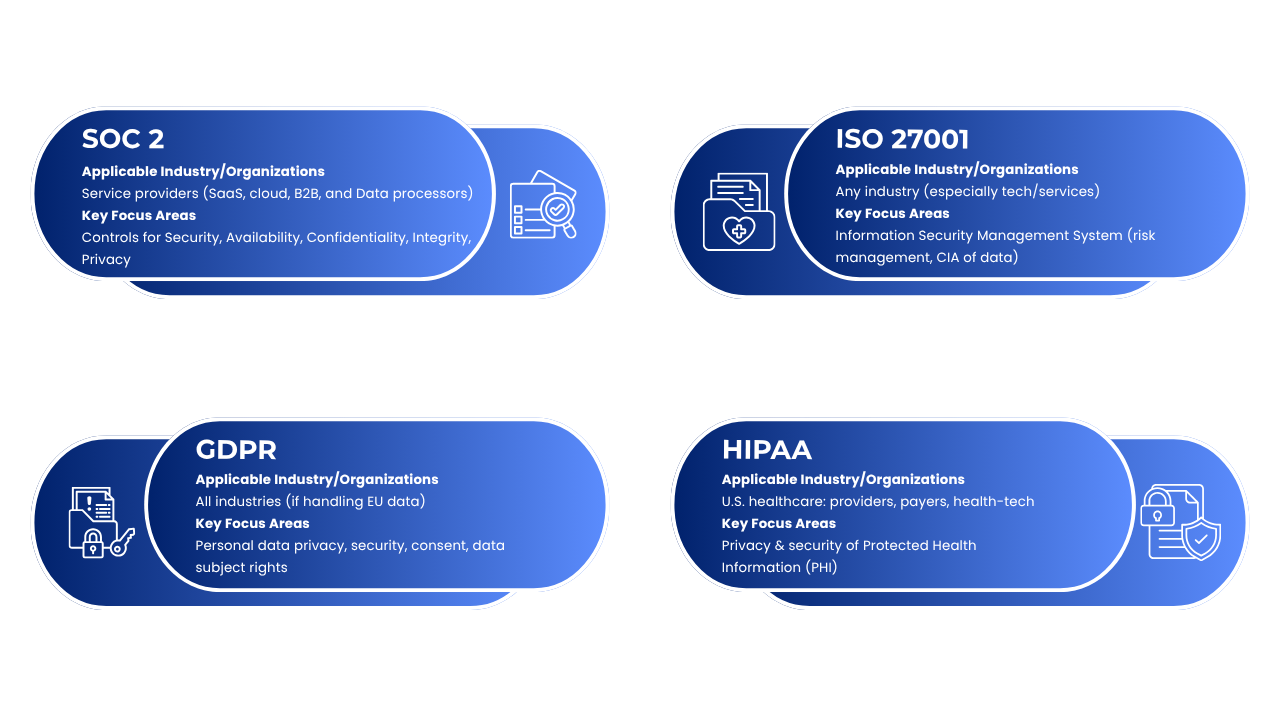
Compliance frameworks are structured guidelines and standards that help companies protect data, manage risks, and meet legal or customer requirements. For tech startups, healthcare entrepreneurs, and e-commerce founders, selecting the right framework is critical: the wrong choice can waste resources, while the right one builds trust and legal assurance. Think of ISO 27001 as one road. SOC 2 shows another way forward. Then there’s HIPAA tighter, focused. GDPR walks its own line across borders. One rule guards patient details. Another watches how info moves globally. Each sets limits based on work type. Who needs what shifts fast. A small app maker may skip some steps. Big clients demand proof sometimes. Matching needs to rule matters most here. Fit drives less stress later. Rules shape around people served usually. Business kind shapes tool choice always.
ISO 27001 Global Standard for Information Security
One way to look at ISO 27001 is as a globally recognized benchmark for handling information safely. What it does is lay out what organizations must do when setting up, running, updating, and refining their ISMS. For real world use, the standard gives companies a flexible structure built around assessing risks tied to data protection. Security here isn’t limited instead, it stretches across human behaviour, operational workflows, and digital tools, aiming always to keep information private, accurate, and accessible.
Any organization (of any size or industry) can adopt ISO 27001. Many tech startups often grab it simply because it shows others they stick to standards used worldwide.
One tool puts everything together risk checks, rules, control steps all lined up neatly inside SOCLY.io. Founders who lack full time compliance help find it easier to manage what needs doing when there is no team around. Paperwork feels lighter. Matching safeguards to requirements stops feeling like a maze.
- Who it’s for: Perfect for businesses aiming to build strong data protection, particularly those in tech or services that work with large clients.
- What it covers: Policies and procedures for risk assessment, asset management, access controls, incident response, and continuous improvement.
- Certification: Organizations can be certified by accredited auditors, demonstrating to customers a formal security program.
SOC 2 – Service Organization Control (Trust) Report
Audit standards called SOC 2 come from the AICPA in the United States. These rules help service businesses protect client information properly. Rather than issuing certificates, auditors give reports after checking control systems against set benchmarks. Reports show if safeguards work as intended.
These criteria are called the Trust Services Criteria (TSC) and include:
- Security (mandatory)
- Availability
- Processing Integrity
- Confidentiality
- Privacy
SOC 2 reports come in two types: Type I (controls at a point in time) and Type II (controls over a period, typically 3–12 months).
Who needs SOC 2?
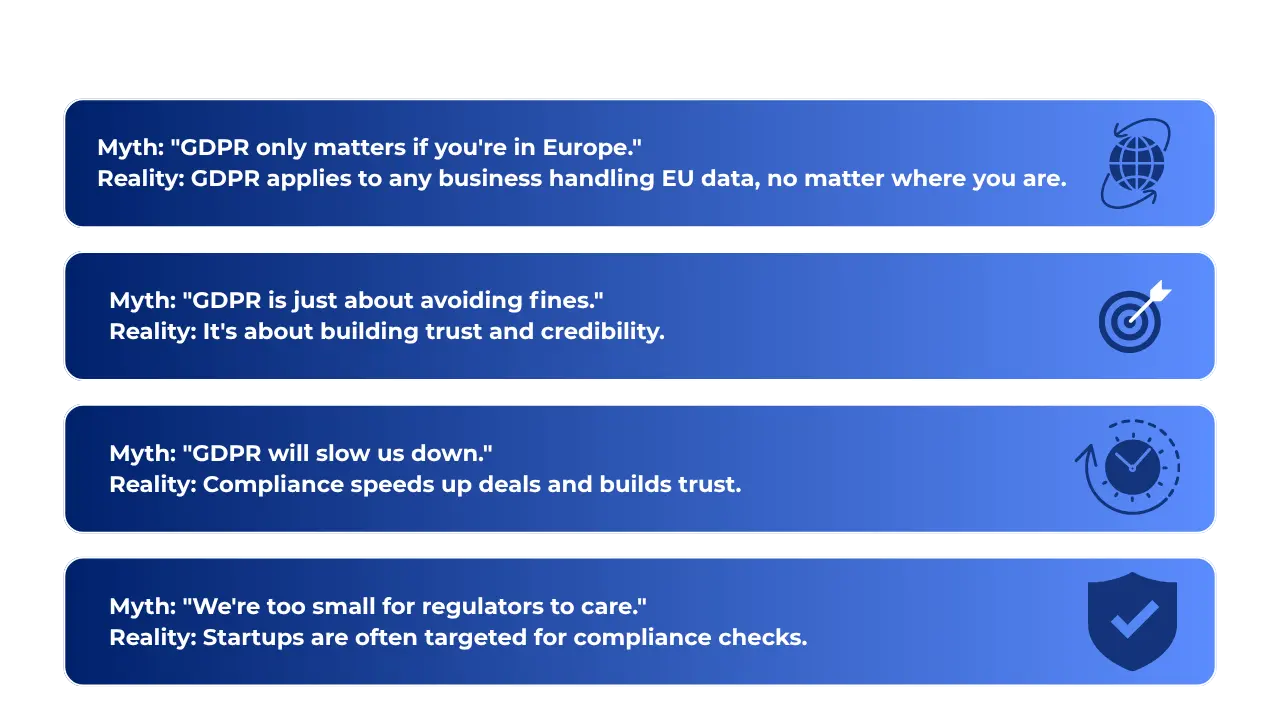
Picture a startup handling user information through its online platform. That kind of company usually needs SOC 2 compliance. Think cloud based tools or software services managing sensitive data. Large businesses tend to request proof before working together. Meeting those expectations means having an audit done. It builds trust when contracts come up for discussion. So firms aiming at corporate clients prepare ahead. Evidence of security practices makes conversations smoother. Without it, deals might stall unexpectedly.
SOC 2 vs ISO 27001:
One way to look at it ISO 27001 sets clear rules worldwide for managing information risk. Meanwhile, SOC 2 checks how well certain safeguards work, especially in American companies. Where ISO demands structure, SOC 2 allows room to adapt. Think of ISO as a full blueprint; SOC 2 more like a custom review. Global reach defines one, regional habits shape the other.
- Who it’s for: Service providers (SaaS, cloud, B2B tech) that handle customer or sensitive data.
- What it covers: Internal controls for data security, availability, confidentiality, integrity, and or privacy.
- Implementation: Define scope, select relevant criteria, implement policies, then hire an auditor.
HIPAA – U.S. Healthcare Data Regulation
HIPAA (Health Insurance Portability and Accountability Act) Most people think it’s optional, but HIPAA isn’t a suggestion it’s a real law made by the U.S. government. Electronic health data gets special protection under these rules, meant to keep private details secure. Doctors, hospitals, insurance companies fall under its reach, along with firms that process claims or manage records. Anyone who works with those groups and touches patient info must follow the same standards, no exceptions.
HIPAA compliance is mandatory for healthcare businesses and vendors. It covers:
- PHI Privacy: Protects all individually identifiable health information.
- Security Safeguards: Requires administrative, physical and technical measures.
- Breach & Consent rules: Dictates how to handle disclosures, authorization and breach notifications.
A health tech or medical startup must follow HIPAA whenever patient information is involved. Handling such data requires checking potential risks, using strong encryption methods. Training team members regularly matters just as much as setting up legal contracts with outside partners. Skipping any part can lead to serious consequences.
GDPR – EU Personal Data Protection
The General Data Protection Regulation (GDPR) EU that guards how private details are used. Anyone, anywhere, dealing with information from people in the EU must follow it. Suppose you work with data keeping it, using it, offering something to those living there even from afar it pulls you into its reach. Being far from Europe does not matter when handling such personal info.
GDPR covers:
- Lawful processing: Legal basis (consent, contract, etc.) for each use of personal data.
- Data subject rights: Right to access, correct, delete, or port data.
- Security and breach notification: Protect data and report breaches quickly.
- Accountability: Document compliance (policies, DPOs, data processing records).
Fines might hit €20 million or climb to 4% of worldwide income making following rules non negotiable. Running an online store? Expect to collect permission before sending promotions, protect shopper details carefully, plus post straightforward privacy terms.
What keeps SOCLY.io useful is how it tracks who said yes to what, logs every step firms take to follow privacy rules. Steps matter when working with people in Europe, since showing proof builds confidence over time. Recording each move helps teams stay clear about their responsibilities, especially around personal information handling.
How to Choose the Right Framework?
Choosing a compliance framework depends on your industry, customers, and the data you handle. Ask:
- Does regulation demand it? (Healthcare = HIPAA, EU customers = GDPR)
- Do customers expect it? (Enterprise SaaS buyers often ask for SOC 2 or ISO 27001)
- What data is at risk? (Personal data = GDPR; PHI = HIPAA; broad security = ISO/SOC 2)
- What resources do you have? (ISO 27001 is more resource heavy, SOC 2 is more flexible)
Begin by checking what could go wrong, pay close attention to customer feedback. Some new companies gradually add structure take a health technology firm, it might start with HIPAA rules, later bring in SOC 2 or ISO 27001 to build stronger safeguards over time.
Running several compliance systems at once? SOCLY.io brings them together so new companies can keep up without extra hassle. Growing faster won’t mean more complexity here.
Implementation Readiness With Tips and Best Practices
- Perform a gap analysis. Start by checking where things stand now. Then measure that against what the framework asks for.
- Define scope clearly. Start by drawing clear lines. Figure out which pieces of your work fit inside. Pick where to focus without guessing.
- Write update policies. Examples: information security, incident response, privacy notices.
- Implement technical controls. Encryption, MFA, monitoring, access controls.
- Train your team. Security awareness, HIPAA privacy rules, GDPR rights.
- Document everything. Policies, training records, risk assessments, audit logs.
- Do internal audits. Fix issues before formal assessments.
- Plan for continuous compliance. Set up ongoing monitoring and reviews.
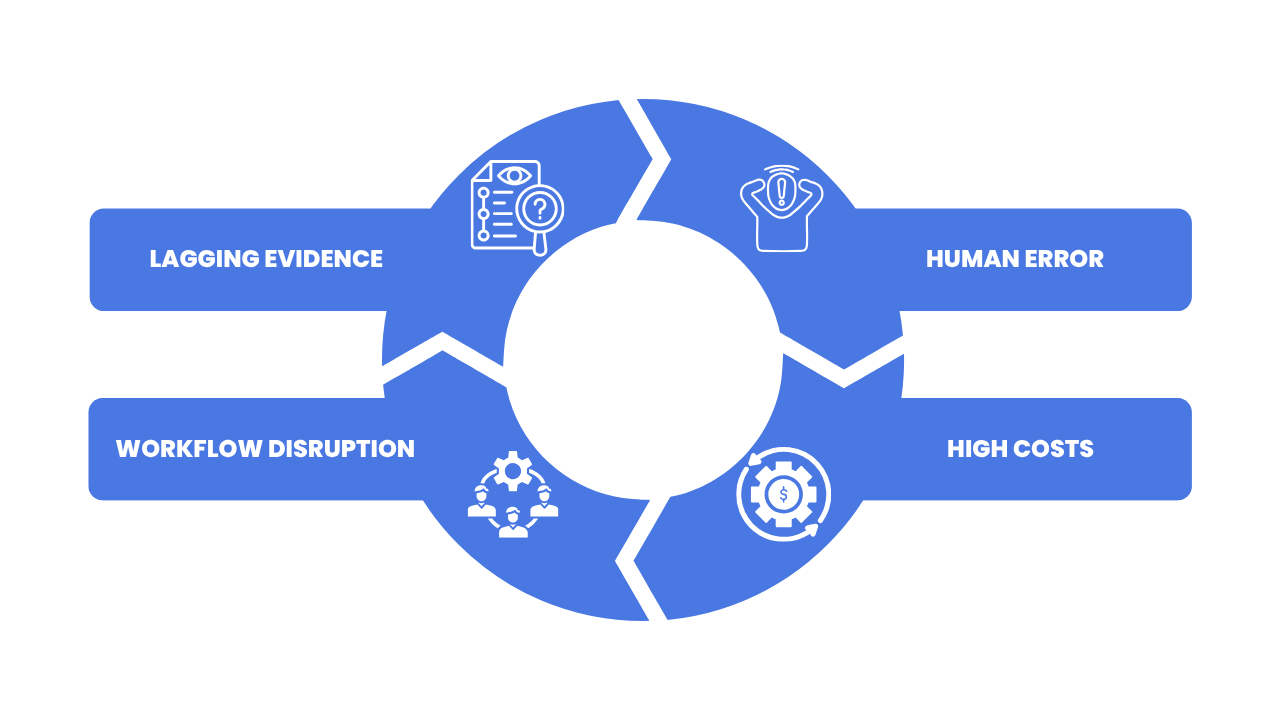
Compliance often seems like a tangled web to startup founders full of rules, proof demands, frequent checks. One wrong turn slows progress. SOCLY.io changes how that works. Instead of juggling separate systems, teams get everything in one place. Think ISO 27001 sitting next to SOC 2, HIPAA lined up with GDPR. Startups move faster when structure isn’t scattered. Growing businesses gain clarity without swapping tools
- Conduct gap analyses with clarity
- Automate evidence collection and policy management
- Track multiple frameworks side by side
- Ready for an audit at any time, so there is no rush when dates approach
Finding it tough to stay compliant? SOCLY.io simplifies the process for small teams, building customer confidence while supporting secure growth.
Depending on how your company operates, what field it’s in, and who your customers are, certain standards will fit better than others. New companies frequently go for SOC 2 or ISO 27001 early on shows they take protection seriously. If health data is involved, following HIPAA rules isn’t optional. For online stores serving Europe, meeting GDPR demands comes first.
A wrong pick might cost you later. Yet going with a solid fit keeps fines away while quietly winning client confidence at the same time. Strength grows where rules are followed well.
Not sure which compliance standard is right for you? Talk to our experts today.