The information security is important for healthtech industry because no one wants to work with an at-risk healthcare provider. However, if someone is looking to use your healthtech services then they would want to know how secure your healthcare organization actually is?
Well, you may think that you have a secure healthcare organization, but this is not always the case. Because with more and more healthcare security breaches that have been reported to the HHS so far, it has become more important than ever for the covered entities and business associates to demonstrate their commitment for keeping “protected health information” secure while providing the top quality healthcare services as well as by putting their patients’ well being first.
What is a SOC 2?
A SOC 2 compliance certificate is perfect for both the covered entities as well as for the business associates that want to reassure their clients that the information they will be providing is secure, available, and confidential. Hence, it has become increasingly common for the organizations that want their vendors to be SOC 2 compliant. Such organizations ask for SOC 2 Compliance to ensure that the healthcare organizations they’re working with have strong security in place.
However, a SOC 2 audit addresses the third-party risk concerns. And, it does so by evaluating the internal controls as well as the policies and the procedures that directly relate to Trust Services Criteria.
So, this means that a SOC 2 audit report focuses on an organization’s non-financial reporting controls which are related to:
- Security,
- Availability,
- Processing Integrity,
- Confidentiality, and
- Privacy of a system.
Security – Is the system you’re using protected against the unauthorized access?
Availability – Is the system that is being used is available for operation and in use as agreed?
Processing Integrity – Is the system processing has been completed and is it valid, accurate, timely, and authorized?
Confidentiality – Is the information that’s designated termed as confidential is actually protected as agreed?
Privacy – Is the personal information that has been collected, used, retained, disclosed, and destroyed in the accordance with the entity’s privacy notice?
However, the responsibilities of the covered entities and the business associates vary and a healthcare organization generally will choose to be evaluated against the security, the availability, and the confidentiality categories. Because if a client can’t be assured that you have reliable and secure processes for securing the protected health information then they wouldn’t choose to work with you.
Why Should Healthcare Organizations Include the Privacy Category?
In addition to choosing the security, availability, and confidentiality categories, for healthcare organizations, it might also make sense to include the privacy category in their SOC 2 audit.
- Let us make you understand this with an example –
Consider a doctor’s office, so what’s one of the first items that the receptionist will hand you? Well, she will hand you “a Notice of Privacy Practices” at first. Do you want to know why?
Well, it is because you’re about to disclose the personal information about your medical conditions to a medical provider. And not just that but you will also provide them with other personal information such as:
- Your data of birth,
- Insurance information, and
- List of medications that you’re on.
But, just imagine if the doctor’s office shares that personal information with a marketing company that want to advertise new prescriptions to you?
And, if the doctor has shared this important information with a research organization which is conducting a research about the treatments for your condition. What if they give that information to other medical providers or to an insurance company?
However, you should be informed that who your personal information they are going to share with.
What are the Benefits of SOC 2 Compliance for a Healthcare Organization?
Well, when a healthcare organization goes through a SOC 2 audit, then it tells that the particular healthcare organization has invested their time, money, and efforts in providing the most secure services to their clients while remaining committed in keeping their clients’ PHI secure.
However, do you know your organizations reputation along with your business continuity, your competitive advantage, your branding, and your patients’ health all depend on the quality of your services and the security of your systems? And, this is the reason why healthcare industry can get benefits from SOC 2 compliance.
- The healthcare industry is based on the customer trust and if a client can’t trust your services, then they won’t choose to use it. For instance, if a patient is victimized because of your lack of due diligence, then do you know what would be the impact to their health and livelihood?
- If your organization has have faced a data breach, then the negative impact of this to your organization’s reputation would be huge. However, if even your healthcare organization has been attacked and the PHI of your patients has been exposed, then it would mean that you will face a lot of obstacles in the path and will have fragmented security.
- In fact, the clients will stop trusting you and the educated prospects won’t want to work with you. And, not just that but the lawsuits and fines will also begin to surface, and patients will also be at the risk of facing the life-threatening consequences.
- Hence, the continuity of your healthtech business and your patients’ well being majorly depends on securing your systems with SOC 2 security compliance.
If you pursue SOC 2 compliance and achieve the attestation then your healthcare organization will have a new branding tool because now you can market your organization by telling that you have reliable and secure services.
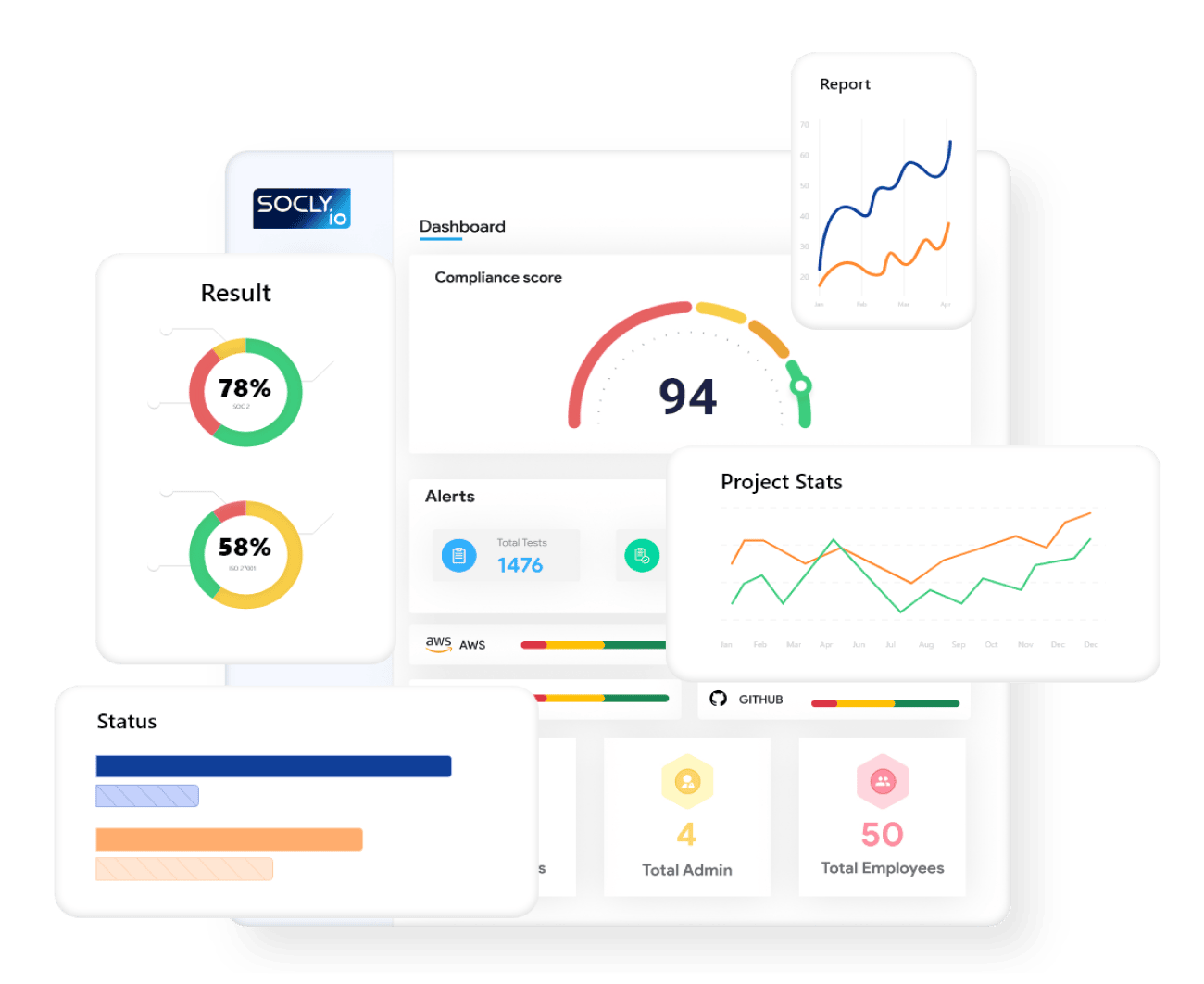
However, when you partner up with an auditing firm such as Socly.io which educates you and performs a quality and thorough audit, then you will gain a valuable competitive advantage.
If your competition doesn’t have a SOC 2 audit report then congratulations you’re ahead of the game. However, even if your competitors have gone through a SOC 2 audit, you should ask yourself that did they go through a quality audit?
But to understand the difference, at first you need to be educated on what a quality audit is so that you can explain to your prospects that why your SOC 2 audit report is more valuable than your competitor’s SOC 2 audit report.
Hence, having a SOC 2 audit report from a licensed and quality-driven firm opens you up to a whole new marketplace of the prospects who are really very knowledgeable about the security and who are looking for a vendor that is SOC 2 compliant.