No business is entirely immune to cyberattacks in this era of digitisation. At least 30,000 websites are hacked daily worldwide, with over half of cybercrimes committed against small to mid-size businesses. While 51% of SMEs do not have cybersecurity measures in place, thinking they are “too small” to get hacked, the average ransom paid by mid-sized organisations in 2021 was $170,404.
Complying with cybersecurity standards has become paramount in determining an organisation’s ability to protect data, prevent financial penalties, build consumer trust, and develop a security culture. The Covid-19 pandemic-related remote working witnessed a 75% spike in daily cybercrime. The pandemic impacted 55% of data exfiltration, 51% of phishing emails, and 35% of ransomware attacks. Consequently, small and medium-sized businesses (SMBs) are increasingly vulnerable to cyber threats due to their laxity in adopting security policies in the pandemic aftermath. Breaches of Personally Identifiable Information (PII), financial information, or Protected Health Information (PHI) can cost the organisation’s reputation and financial loss. Thus, adhering to regulatory standards and protecting the Confidentiality, Integrity, and Availability (CIA) of information is necessary.
Benefits of Cybersecurity Compliance for your business
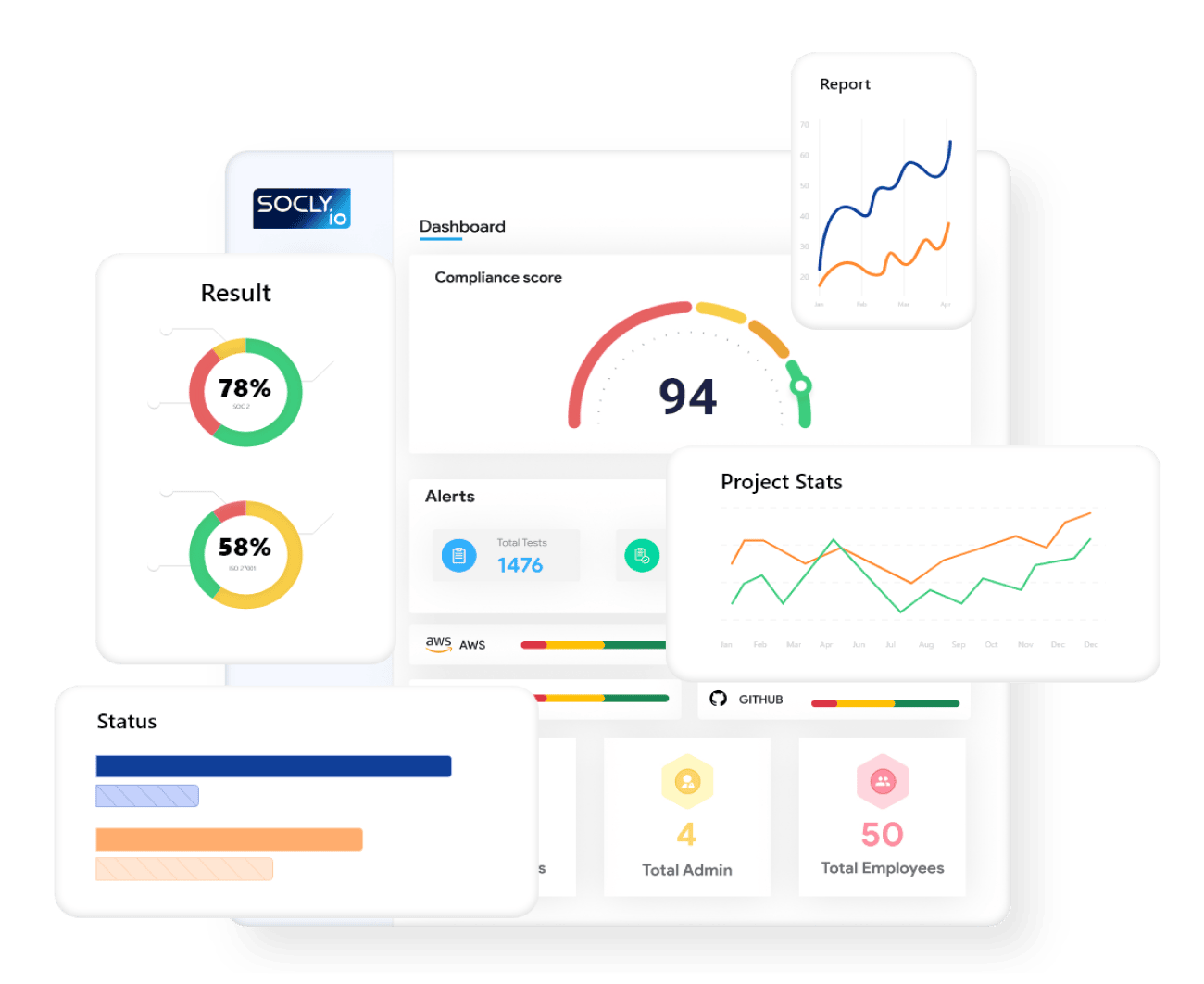
Cybersecurity compliance involves aligning an organisational risk management framework with pre-defined security measures to implement a systematic risk governance approach and rule out potential vulnerabilities that may affect the company, customers, and stakeholders. Meeting data security standards of SOC2, ISO 27001, PCI-DSS, HIPAA, CCPA and other major regulatory frameworks help your business identify, interpret, and combat cyber threats and protect your intellectual property, garnering consumer confidence and loyalty. The multi-faceted benefits of developing a resilience-focused “prescriptive” security posture for your organisation are as follows.
Improves data management capabilities
Businesses should plan to store sensitive client information on secured digital platforms to promote privacy. Data stored at the organisation’s existing software infrastructure or cloud-based solutions must be accessible only to authorised administrators. Integrating data management capabilities with cybersecurity tools helps prevent unauthorised access, malware attacks, and data breaches while ensuring confidentiality and integrity in the industry landscape.
Promotes operational efficiency
Organisations using security technologies can manage excess data, expose privacy loopholes, identify wasted assets, implement new resources to improve operational efficiency, and reduce unnecessary data usage by eliminating noise and focusing on the core. Investing in cybersecurity programs strengthens the overall organisational infrastructure and helps combat vulnerabilities that allure hostile actors.
Facilitates industry-standard practices
Adopting security practice standards helps your organisation’s IT team, compliance officers, and supervisors assess risks, diminish errors within the processes, avoid misinterpretations, and make relevant decisions with a simplified and optimised workflow. Such unified cybersecurity policies make B2B and B2C service transactions more customer-centric and fulfil user expectations while saving valuable resources.
Prevents fines and penalties
Failure to comply with appropriate security regulations can incur hefty financial penalties for businesses. Almost all regulatory authorities charge costly compensation for organisations that do not strategise strict corporate governance and consumer protection policies. HIPAA charges $100 to $50,000 per violation of security norms, while Payment Card Industry Data Security Standard (PCI-DSS) penalises the organisation with fines between $5,000 and $100,000 per month.
Builds security culture
A Verizon 2022 report says 85% of data breaches in organisations involve a human element. While external cloud assets encounter the most malicious invasions, passwords and credentials are the most sought-after data types in cyberattacks. Thus, developing a security culture across departments and workflow management systems helps employees to indulge in safe digital practices and refrain from risky behaviour. Organisations having a robust security framework train their employees with relevant skills and knowledge to identify safety breaches and follow appropriate measures to protect sensitive data.
Develops consumer trust and brand reputation
The cost of the threat posed by cyberattacks and data breaches is not limited to business interruption and financial loss. The lack of efficient cybersecurity protocols irreversibly damages your brand reputation and repels consumers. 78% of consumers stop engaging digitally with a brand that suffered data breaches, while 36% turn away entirely. Consumers prefer to put their trust in businesses that nurture cybersecurity compliance and maintain confidentiality effectively. Strong security governance portrays your business as trustworthy and builds consumer confidence and brand image.
The bottom line
It would be best to watch out for tech support fraud, identity theft attempts, social engineering attacks, and other sophisticated threats besides malware, ransomware, and phishing attacks. The digital world witnesses a cyberattack every 44 seconds that impairs business performance and incurs a financial loss. Thus, developing a comprehensive cybersecurity foundation that complies with the standard regulatory protocols is necessary to promote operational efficiency, prevent fines and penalties, protect confidential data, and gain consumer trust.
Times of India:https://timesofindia.indiatimes.com/blogs/voices/cybersecurity-compliance-a-necessity-for-your-business/
SOCLY.io for Singapore – Presenting at Cyber Security World, Asia, Marina Bay Sands this October 12-13.
Cyber Security World, Singapore, Asia’s most exciting cybersecurity event on 12th – 13th October 2022 for its 8th edition at Marina Bay Sands, Singapore. The
- June 20, 2024